CVE-2017-7253
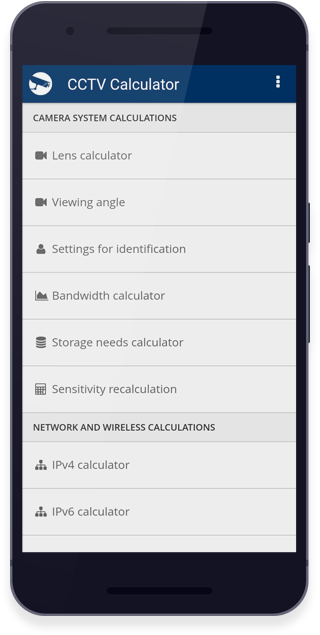
Dahua IP Camera devices 3.200.0001.6 can be exploited via these steps: 1. Use the default low-privilege credentials to list all users via a request to a certain URI. 2. Login to the IP camera with admin credentials so as to obtain full control of the target IP camera. During exploitation, the first JSON object encountered has a "Component error: login challenge!" message. The second JSON object encountered has a result indicating a successful admin login.
BID: http://www.securityfocus.com/bid/97263
MISC: https://gist.github.com/anonymous/16aca69b7dea27cb73ddebb0d9033b02
CVE: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7253
published: 30. 3. 2017